Anthropic's Mythos Uncovered Decades-Old Vulnerabilities. Your Governance Model Needs to Catch Up.
Project Glasswing just exposed thousands of zero-days across every major OS and browser. Here’s what that actually means if you ship AI agents in regulated industries.
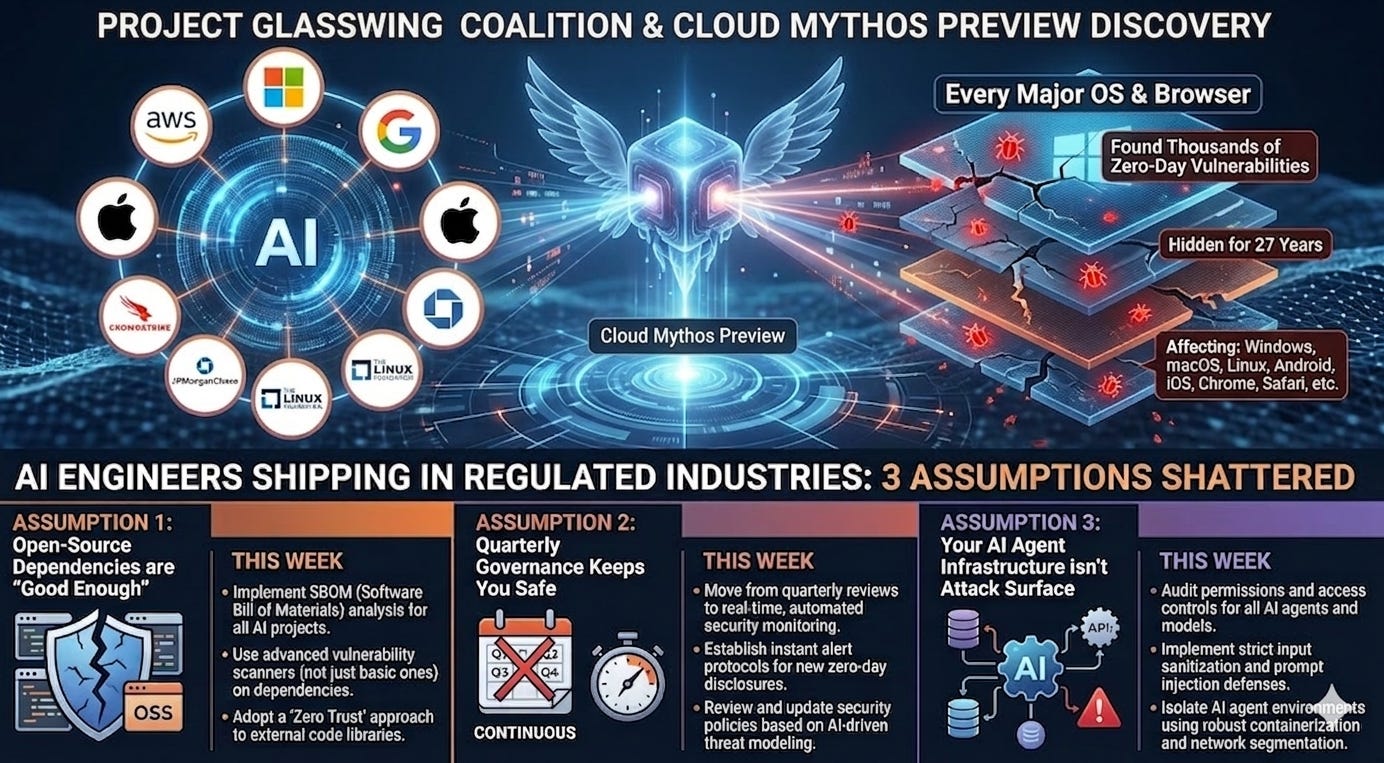
TL;DR - Anthropic’s Project Glasswing coalition — AWS, Microsoft, Google, Apple, CrowdStrike, JPMorganChase, the Linux Foundation, and six others — used an unreleased model called Claude Mythos Preview to find thousands of zero-day vulnerabilities across every major OS and browser, some hidden for 27 years. For AI engineers shipping in regulated industries, this breaks three assumptions simultaneously: that your open-source dependencies are “good enough,” that quarterly governance keeps you safe, and that your AI agent infrastructure isn’t attack surface. Here’s what to do about each, this week.
The 27-Year Bug and the Five-Million-Test Miss
Let me start with the two numbers that should keep you up tonight.
Twenty-seven years. That’s how long a remote crash vulnerability survived in OpenBSD — an operating system whose entire reputation is built on being security-hardened. It runs firewalls. It runs critical infrastructure. Mythos Preview found it.
Five million. That’s how many times automated security tests hit the vulnerable line of code in FFmpeg without catching the bug. Mythos Preview caught it on what amounts to a first read.
These aren’t edge cases. These are the libraries underneath your production systems right now.
Project GLASSWING
Three Things That Just Broke
Enterprises started deploying AI across healthcare, financial services, airlines, and other regulated industries. These are the industries where you don’t get to say “we’ll patch it next sprint” — you answer to regulators, patients, and auditors. Glasswing broke three foundational assumptions we see in nearly every deployment we touch.
Broken Assumption #1: “We Track Our Dependencies”
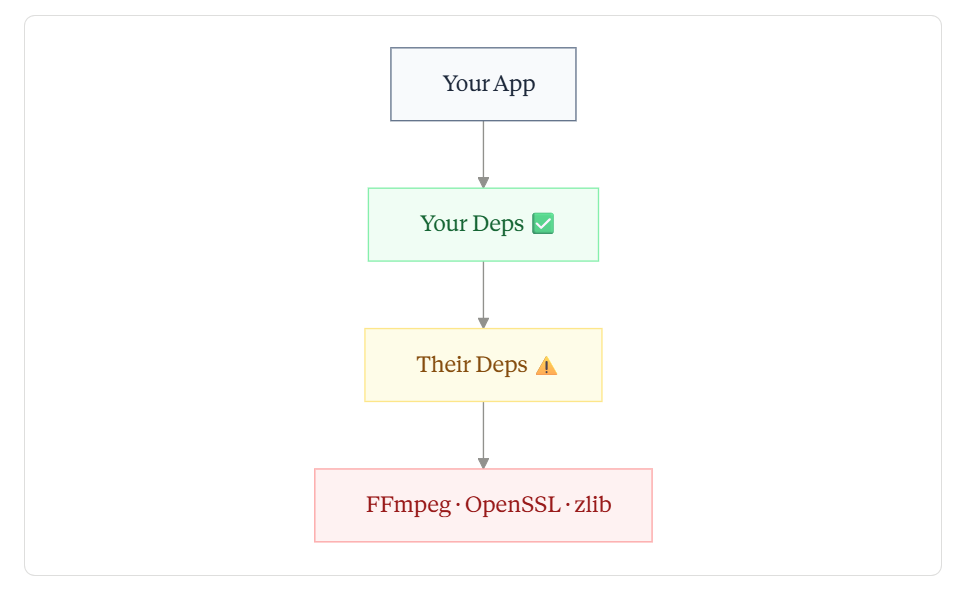
You track your direct dependencies. Maybe your first layer of transitive dependencies. But Glasswing exposed vulnerabilities in the deep layers — the FFmpegs and OpenSSLs and zlibs that your dependencies’ dependencies depend on.
The deeper you go, the less you track — and that’s where Mythos found the bugs.
The Linux Foundation joined Glasswing because the people maintaining the software at the bottom of that chain don’t have security teams. Your SBOM was a compliance artifact. It needs to become an operational dependency map with patching SLAs attached to every node.
Broken Assumption #2: “Our Governance Cadence Is Sufficient”
CrowdStrike’s CTO said it plainly: what once took months now happens in minutes. Mythos Preview autonomously chained together multiple Linux kernel vulnerabilities to escalate from user to root — no human steering required.
Your quarterly vulnerability review doesn’t survive this. You need dependency scanning on every build, and a fast-track patching path that bypasses the standard change advisory timeline for critical zero-days.
Broken Assumption #3: “Our AI Agent Layer Isn’t Attack Surface”
This is the one nobody’s talking about, and it’s the one I see every day.
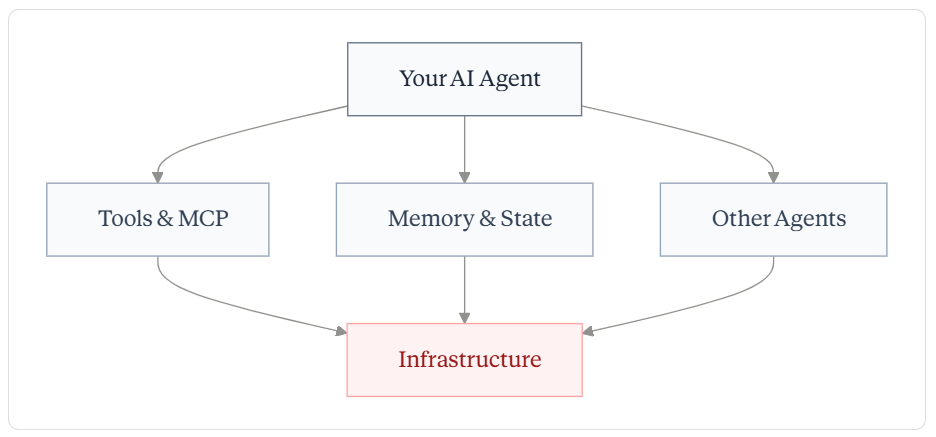
If you’re building multi-agent systems — agents calling tools via MCP, persisting memory, chaining decisions across services — you’ve built execution paths that no traditional penetration test covers.
Traditional security tests the infrastructure. Nobody tests the agent paths that sit on top of it.
Here’s the connection nobody’s making: the agentic reasoning that lets Mythos Preview autonomously chain kernel exploits is architecturally the same capability your agents use to chain tool calls. If a compromised dependency injects malicious context into your agent’s execution chain, what layer catches it?
For most systems? Nothing. The guardrails check the model’s outputs. They don’t check what flows into the model from compromised upstream tools.
Your Playbook: This Week, This Month
This Week
Map your Glasswing exposure now. Anthropic published cryptographic hashes of unpatched vulnerabilities. When full disclosures land, you need to already know your dependency overlap. Don’t start the audit after the CVEs drop.
Benchmark your real patching SLA. Not the number in your security policy — the actual elapsed time from “critical zero-day announced” to “patched in production.” If it’s measured in weeks, you’ve found the gap.
Tabletop an AI-speed attack. Get your security, platform, and AI engineering leads in a room. Scenario: a Mythos-class model finds a zero-day in a dependency your agents use. An exploit is weaponized in hours. Walk through your response. Find where it breaks.
This Month
Shift SBOM from compliance to CI/CD. Dependency scanning on every build. Automated alerts when any dependency matches a Glasswing disclosure. No exceptions.
Audit your agent attack surface. Document every tool-calling interface, memory layer, and cross-agent trust boundary. Test what happens when one node in the chain serves compromised context.
Design a fast-track patch path. Your standard CAB process can’t be the only route for critical zero-days.
The 90-Day Clock
Anthropic committed to publishing findings within 90 days — vulnerabilities fixed, lessons learned, and recommendations for how security practices should evolve. They’re working on guidance covering disclosure processes, patching automation, supply chain security, and standards for regulated industries.
That 90-day report will matter. But the vulnerabilities exist now. The exploitation tools are advancing now. And the gap between AI-speed offense and quarterly-cadence defense is only getting wider.
The Glasswing butterfly hides in plain sight — transparent wings, invisible against the forest. These vulnerabilities did the same thing for decades. The question isn’t whether your systems are affected. It’s whether your response will move at the speed this moment demands.